Simulate Phishing Attacks
In today’s environment, social engineering attacks are prevalent and increasing. The human element is often the weakest component in a company’s security defense. With PhishingBox, you can easily conduct simulated phishing attacks to test employees' security awareness as part of a comprehensive human risk management, and expand beyond the inbox with callback phishing scenarios. For a deeper look at how we handle the training experience during a simulated phishing attack, explore Phishing Training. Our Phishing Simulator allows you to create custom groups with as many phishing targets as you would like and sync your target database using our API and webhook integrations.
-
Individuals
Target specific employees with tailored spear phishing attacks.
-
Groups
Test a group of employees with targeted phishing campaigns.
Phishing Template Editor and Library
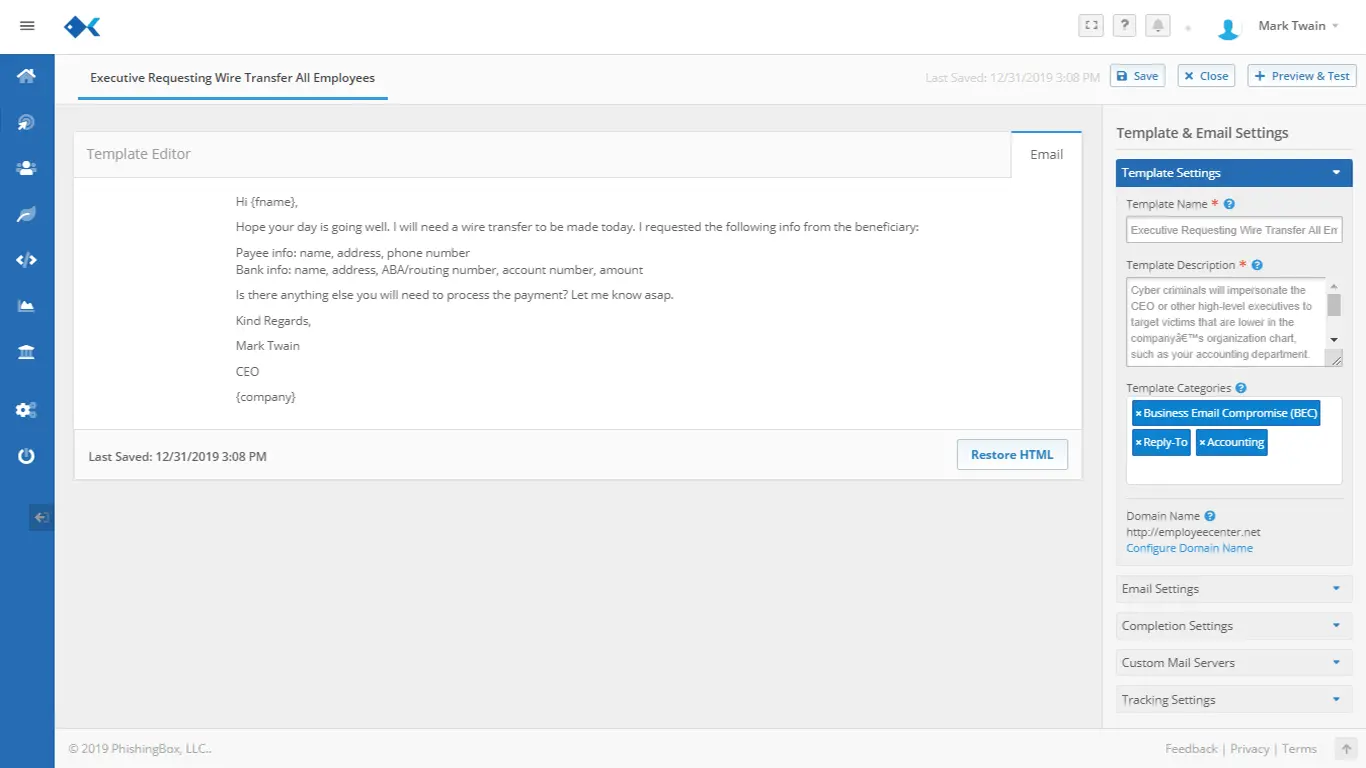
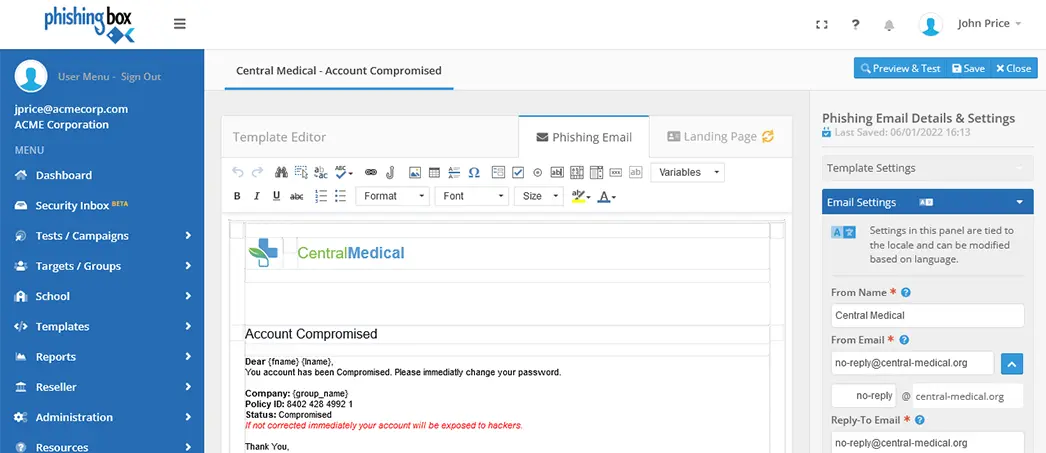
Our AI-powered, intuitive editor and robust library provides you with everything you need to exercise full control over your social engineering testing and customize it end-to-end. Learn more about the Template Editor.
Now with AI instrumentation features, build your own custom phishing templates with Bootstrap support. Utilize our visual editor, asset hosting, and more. We have custom CNAME support for your own phishing domain, and each template is comprised of an email and a landing page that can be accompanied by a training page, all of which you can customize.
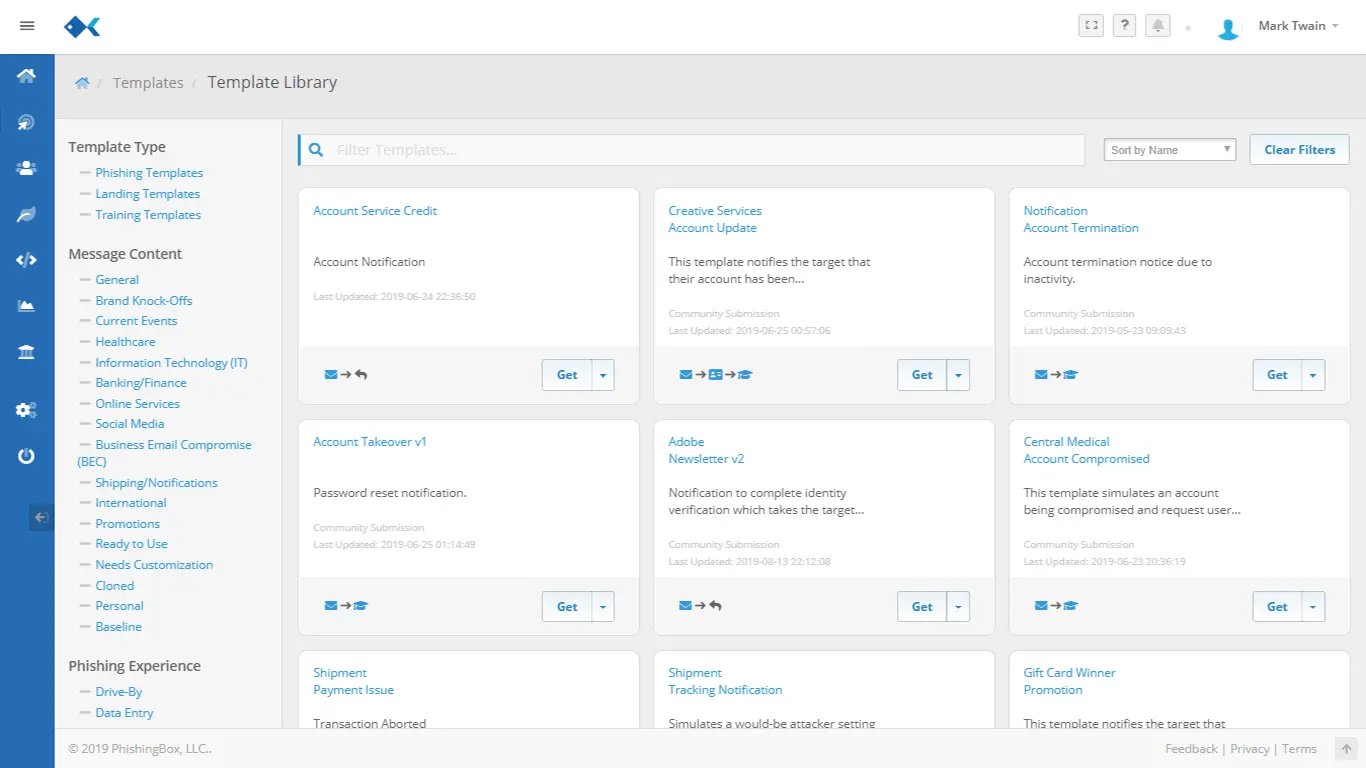
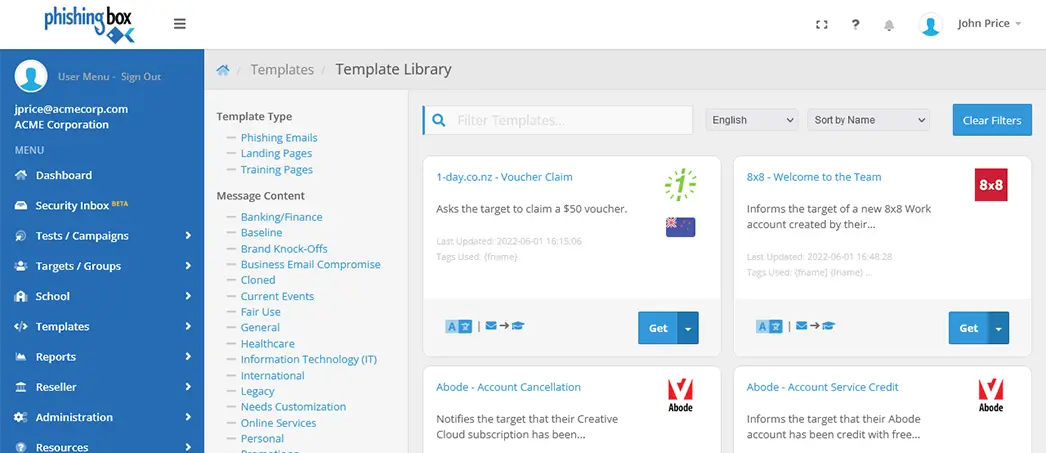
The Phishing Simulator includes a vast library of templates designed to mimic real-world attacks without any of the danger. Our Phishing Template Library also includes our community of users who have submitted their phishing templates for shared resource use.
Target and Group Management
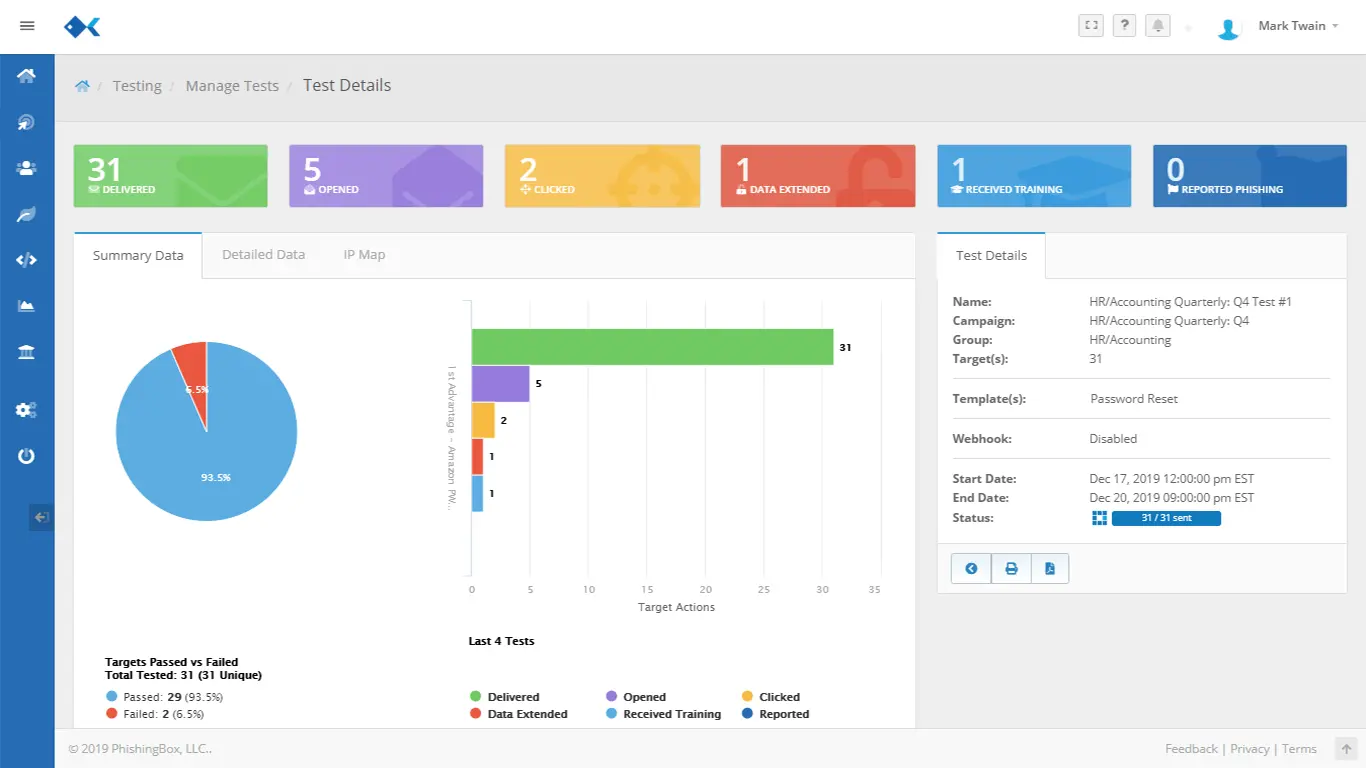
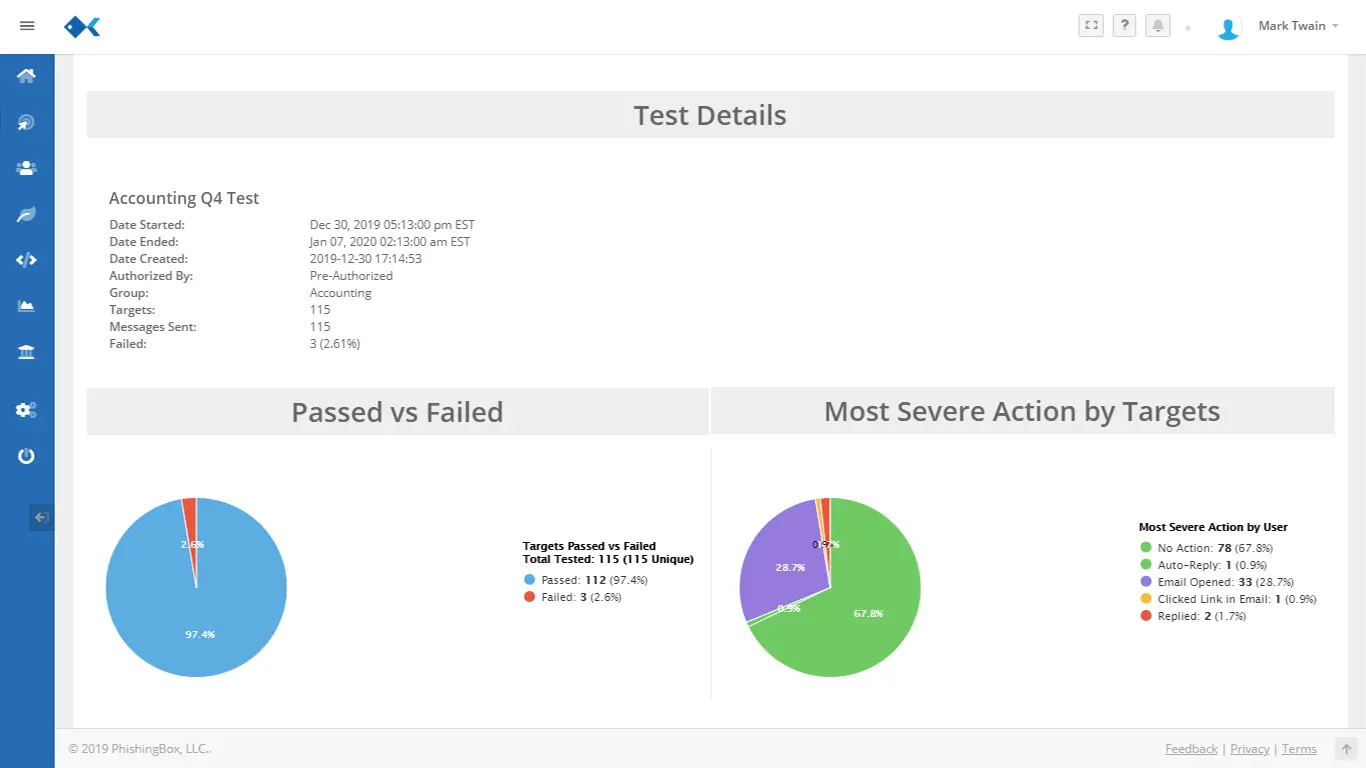
Testing your employees with simulated phishing attacks is an important part of your overall cybersecurity training program. PhishingBox makes it easy to measure and demonstrate your employees’ aptitude and progress on highly visual dashboards and reports, while vetting for false positives with Advanced Human Detection (AHD). Your employees are on the frontline in the anti-phishing battle and you can’t win without them.
-
Groups
Test a group of employees' efficacy with targeted phishing campaigns.
-
LDAP Integration
Fully supports the Microsoft Lightweight Directory Access Protocol.

Phishing Simulator Features
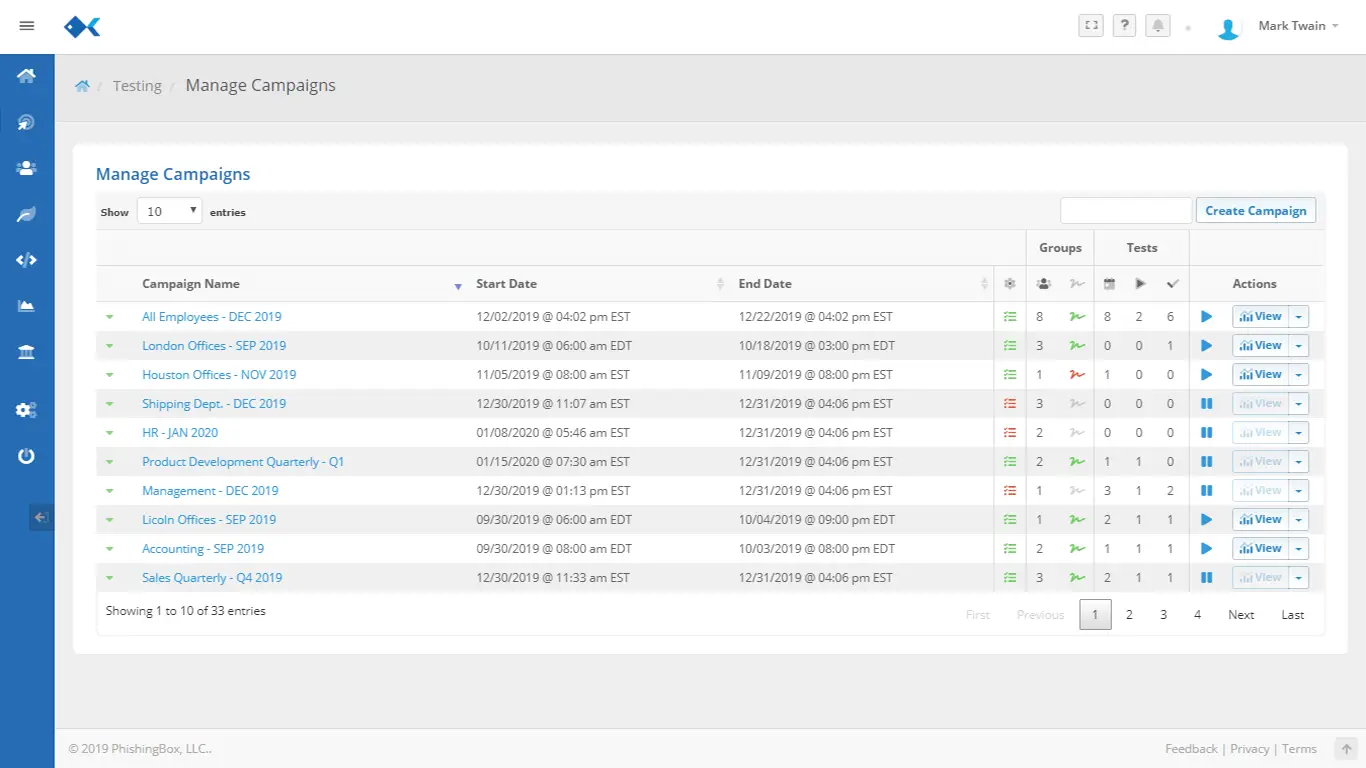
Build realistic phishing campaigns, manage targets at scale, customize the full target experience, and connect failed tests to training, reporting, and managed support.
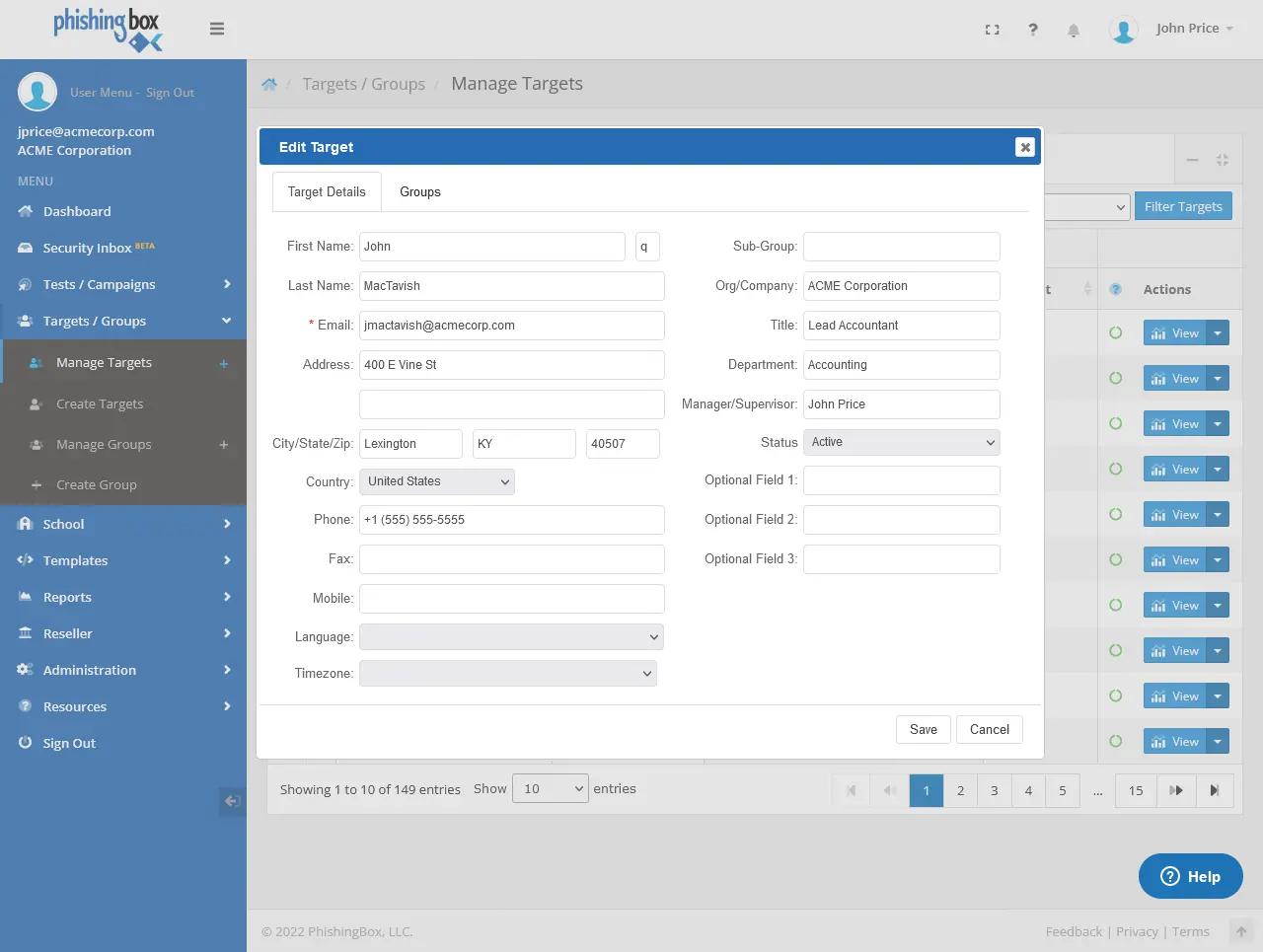
Simple Target Management
Sync with third-party sources to keep target lists current and automatically add new targets to scheduled tests.
Template Library
Start with ready-built phishing templates from an extensive library or customize them to match your own campaigns.
Robust Template Editor
Customize email content, landing pages, training moments, and the full target experience from one editor.
Phishing Training
Take a deeper look at the landing pages, training moments, and guided user experience that follow a failed simulation.
Training Emails
Reinforce secure behavior between simulations with lightweight email-based awareness content that supports your campaigns.
Managed Phishing Services
Let our team run the simulator for you with campaign planning, execution, reporting review, and program guidance.
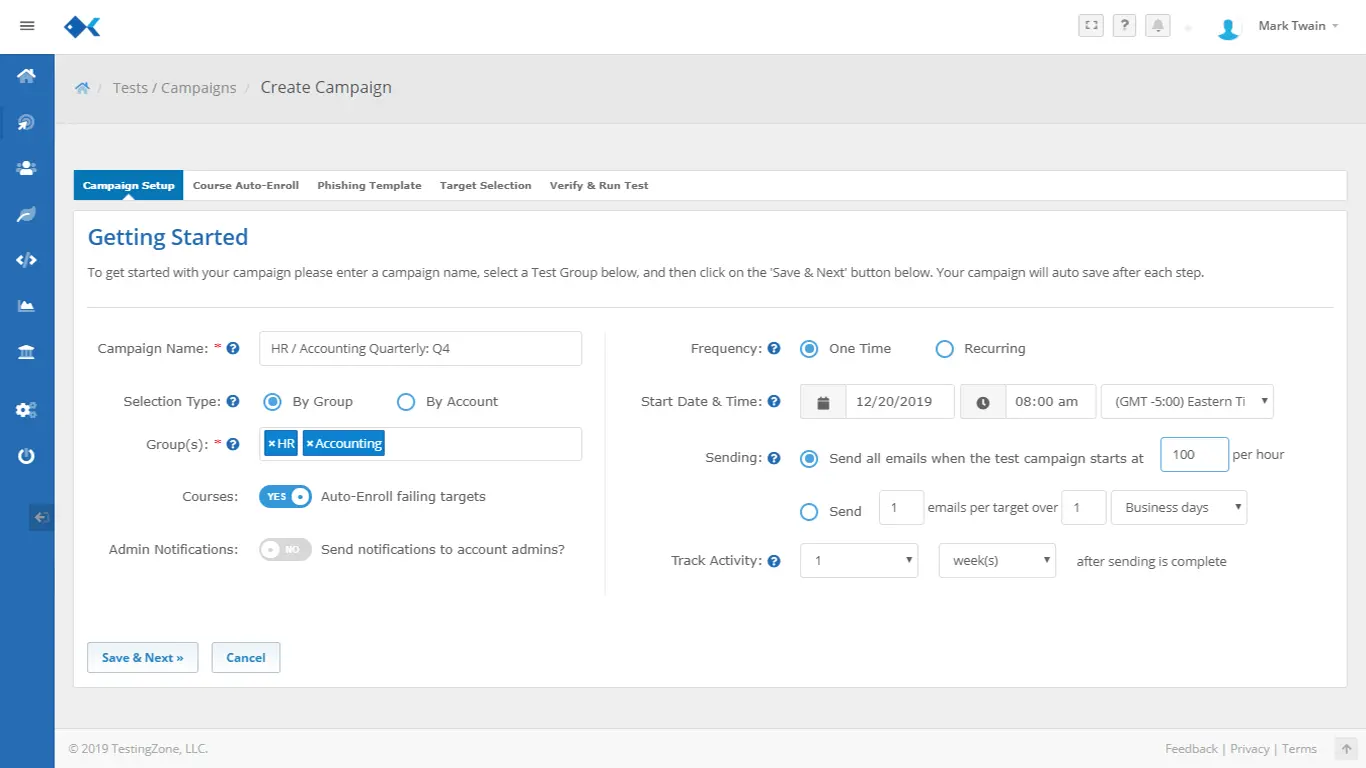
Campaign Wizard
Schedule 12 months of realistic phishing simulations that align with your organization's cadence and program goals.
Callback Phishing
Extend phishing simulations beyond email with callback scenarios that push targets into a phone-based social engineering test.
Real-time Notifications
Alert targets when they fail tests and keep administrators and clients updated on campaign status as events happen.
Training Content
Blend built-in content with training from leading providers so teams always have fresh material ready to assign.
Advanced Human Detection
Use advanced analysis methods that make phishing simulation testing more manageable, accurate, and defensible.
Reporting
Generate branded reports that highlight campaign results, trends, and metrics in the format your stakeholders need.
Support
Work with a US-based support team that can help with phishing simulation planning, troubleshooting, and rollout questions.
Questions Teams Ask About Phishing Simulator
Get a quick view of how PhishingBox handles templates, scheduling, follow-up training, reporting, and LMS compatibility for phishing simulation programs.
Are the phishing templates and scenarios updated, and are new scenarios added according to current trends in phishing attacks?
You can fully customize any of our existing scenarios and phishing campaigns to fit your exact needs and language preference. We also constantly add new scenarios according to current trends in phishing attacks and cybersecurity. These are also fully customizable and editable. Alternatively, you can easily create templates and scenarios from scratch.
Is all training material provided by PhishingBox or do you have access to third-party content?
The platform includes training from PhishingBox and other third-party content providers.
Can we schedule phishing campaigns in advance?
Yes. The phishing simulator allows for custom scheduling of phishing campaigns.
If someone fails a phishing test, will they automatically be enrolled in training?
Yes. There are several options for delivering training if a user fails a phishing test. One method is to provide a training moment as soon as the user fails a test. In addition, a user may be enrolled automatically into a training course or program should they fail a test.
Does the simulator include a reporting plugin or method for users to report a phishing email?
Yes. We include our KillPhish plugin to allow users to report phishing emails, including simulated phishing emails. If an end user reports a training email it is recorded as part of the NRS or Net Reporter Score metric.
Additional Resources
PhishingBox Ecosystem
This brochure provides an overview of the PhishingBox security awareness ecosystem.
DownloadBusiness Case
This document provides an overview of the benefits of using PhishingBox's Phishing Simulator and ongoing cybersecurity training.
DownloadPrevention Checklist
This document outlines controls that should be implemented to prevent or minimize phishing attacks.
Download