Facebook Phishing Scams
Learn how to spot Facebook phishing scams, fake Meta business alerts, and redirect-based login attacks, plus what to do if you click a suspicious link.
Originally published February 2024 - updated May 2026 with refreshed guidance on current Facebook phishing tactics, reporting steps, and business account risks.

Facebook remains one of the most frequently targeted platforms for phishing and social engineering attacks. Cybercriminals continue to develop new techniques to impersonate Meta, steal login credentials, and compromise both personal and business accounts. This 2026 refresh highlights recent Facebook phishing scams, including campaigns that target business users, and provides practical steps to protect your organization.
Recent Facebook Phishing Scams
1. Redirect Abuse Using Facebook's Warning Pages
Recent research uncovered attacks using Facebook's own external-link warning pages to make malicious links look more trustworthy. Attackers build redirect chains that start from Facebook's legitimate interface, making users more likely to trust the next click. Meta explains how its suspicious-link warnings work in its link safety guidance.
How the scam works
- Attackers register benign-looking domains such as
thebeachvilla.co.zaoromniotech.co.uk. - These domains host scripts that redirect users through Facebook's warning page.
- After the user clicks "Continue," they land on a fake Facebook login page designed to steal credentials.
- After harvesting credentials, the victim is redirected to the real login page to reduce suspicion.
- Campaigns are highly customized by language and urgency, often claiming "unusual activity detected."
Why this matters
This tactic blends platform-level trust with social engineering, making the attack harder to spot. Even users who are security-conscious may assume the link is safe because Facebook generated the warning dialog.
2. Fake Facebook Business Pages Flooding Users With Phishing Messages
Another major development is a surge in phishing attacks targeting Facebook Business Pages, advertisers, and social media managers - an area that attackers increasingly view as high-value.
What security researchers found
- Attackers create new Facebook Business Pages that mimic official Meta branding.
- These pages then send phishing emails from the legitimate domain
facebookmail.com. - Messages falsely claim account violations, ad policy issues, or eligibility for benefits like "free ad credit."
- One campaign generated over 40,000 phishing emails, with individual businesses receiving thousands in a short time.
Check Point Research described a 2025 campaign targeting Facebook Business users with messages sent through the legitimate facebookmail.com domain in its November threat intelligence report.
Why businesses are vulnerable
Social media managers and advertisers rely on Facebook for daily operations, so urgent messages about policy or ad spend feel believable. The use of Meta's real email domain further increases trust.
Common Facebook Phishing Scams Still Active
Even as attackers adopt new methods, many longstanding tactics continue to affect users:
- Compromised accounts posting emotionally charged links ("I can't believe what happened...") that lead to credential-harvesting sites.
- Direct messages from compromised friends encouraging users to click malicious links.
- Fake security alerts claiming someone else attempted to log in.
- Giveaway, prize, or gift card scams impersonating popular brands.
These persistent tactics continue to succeed because they rely on urgency and familiarity.
The Risks: Why Facebook Phishing Is More Than Just a Social Media Problem
A compromised Facebook credential can lead to:
- Access to Instagram, Messenger, and connected apps
- Control over business pages, ad accounts, and audiences
- Unauthorized ad spending or scams targeting customers
- Social engineering attacks against employees
- Lateral movement into work-related systems via reused passwords
For organizations, the business-page phishing wave is especially dangerous, as attackers often aim to monetize accounts or distribute scams at scale.
How to Protect Users and Organizations From Facebook Phishing
1. Enable Multi-Factor Authentication (MFA) on all accounts
MFA drastically reduces account-takeover attempts, even when credentials are stolen.
2. Use a password manager to avoid fake login pages
Password managers auto-fill credentials only on legitimate domains - an excellent defense against redirect-based phishing.
3. Train employees to recognize Facebook-themed phishing
Focus on:
- Avoiding unexpected "policy violation" messages
- Verifying links by navigating directly to Facebook.com
- Reviewing business page email alerts carefully
- Questioning messages that create urgency
- Double-checking external-link warnings
4. Monitor Business Pages and ad accounts for changes
Facebook Business accounts should be monitored just like any other business-critical platform. Watch for:
- New admins added
- Sudden ad spending changes
- Suspicious page posts
- Security or recovery email changes
5. Use simulated phishing to reinforce awareness
Social-media-themed phishing simulations help employees practice identifying deception. Platforms such as PhishingBox pair realistic scenarios with cybersecurity training and just-in-time coaching that reinforce safer behavior after a click.
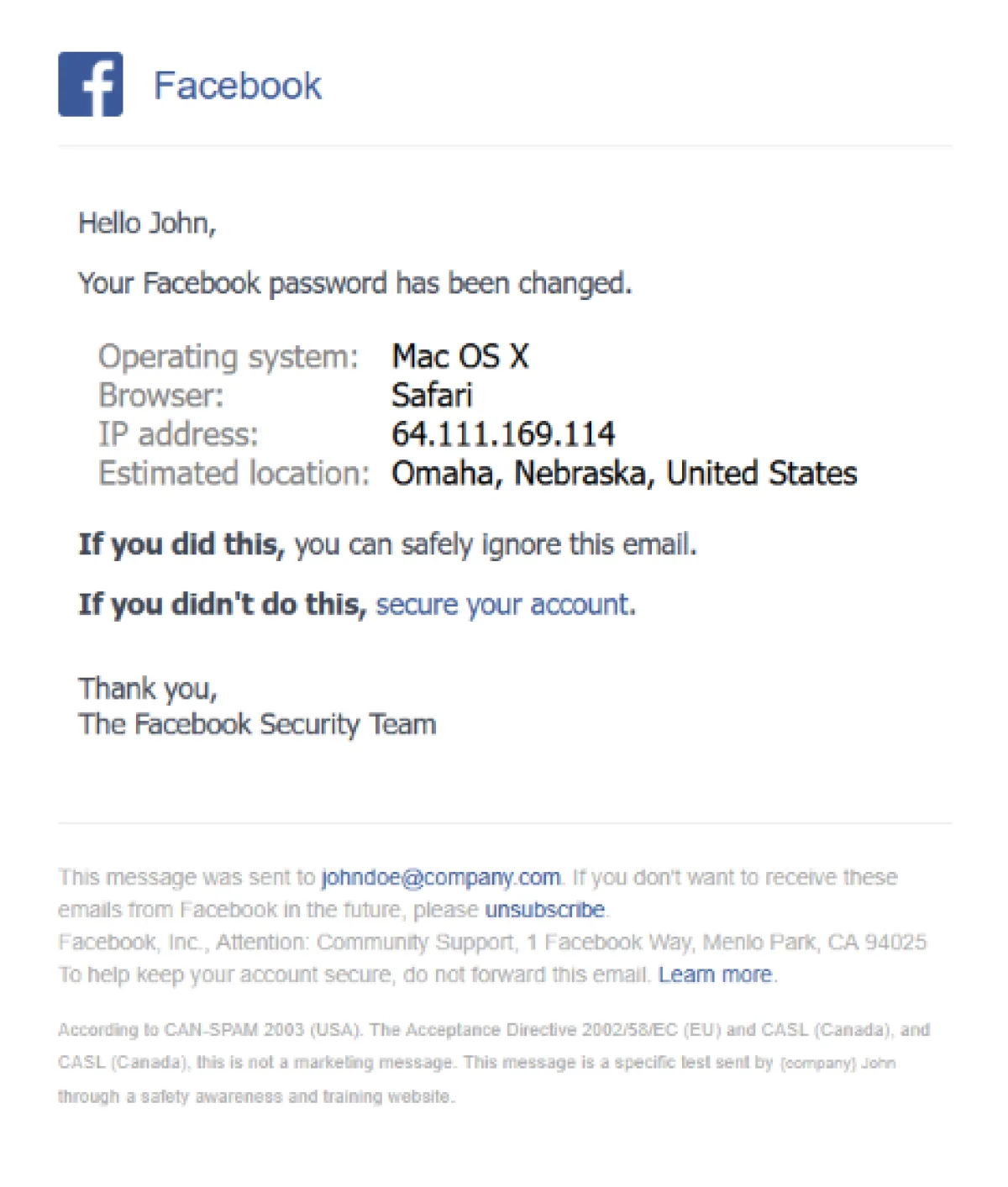
Example of a PhishingBox Facebook-themed phishing template used in user awareness training.
How to Tell if a Facebook Email Is Legitimate
If a message claims to be from Facebook or Meta, start by confirming it through official channels instead of the email itself.
- Check whether the alert also appears in Facebook or Business Support Home after you sign in directly.
- Treat display names and sender domains as only one signal. Attackers sometimes abuse trusted delivery paths, so domain trust alone is not enough.
- Hover or long-press links before clicking and look for destination domains that do not belong to Facebook or Meta.
- Be skeptical of urgent policy, copyright, ad credit, or account recovery notices that push immediate action.
Meta's official guidance on suspicious Facebook emails is a strong reference point for employees and admins.
What to Do if You Clicked a Facebook Phishing Link
If you clicked a suspicious link or entered your credentials, act quickly:
- Change your Facebook password immediately from a direct login session.
- Review active sessions, business page admins, ad account permissions, and recovery email settings.
- Reset reused passwords on any other accounts that shared the same password.
- Enable MFA if it is not already on.
- Report the incident internally so your organization can watch for follow-on fraud or impersonation.
Meta also provides step-by-step guidance for recovering a phished Facebook account.
How to Report Facebook Phishing to Meta
Reporting suspicious Facebook phishing helps limit the lifespan of malicious pages and messages.
- Forward suspicious emails to
phish@fb.com. - Use Facebook's in-product reporting tools for scam pages, messages, and posts.
- If the message targets a business account, verify account health through Business Support Home before taking any action.
- Preserve the phishing email, URL, and screenshots for your security team or incident response process.
Meta's March 11, 2026 anti-scam update outlines newer platform defenses and warning systems.
Conclusion
The latest Facebook phishing scams demonstrate how quickly attackers adapt. What used to be simple credential-stealing pages has evolved into redirect abuse, impersonation of Meta business infrastructure, and high-volume campaigns targeting advertisers and organizations.
By combining MFA, password managers, internal monitoring, and regular phishing awareness training, individuals and businesses can significantly reduce the risk of compromise.